CIIP FAQ
Find more information about CIIP
WHICH SECTORS FALL WITHIN THE SCOPE OF THE CIIP LAW?
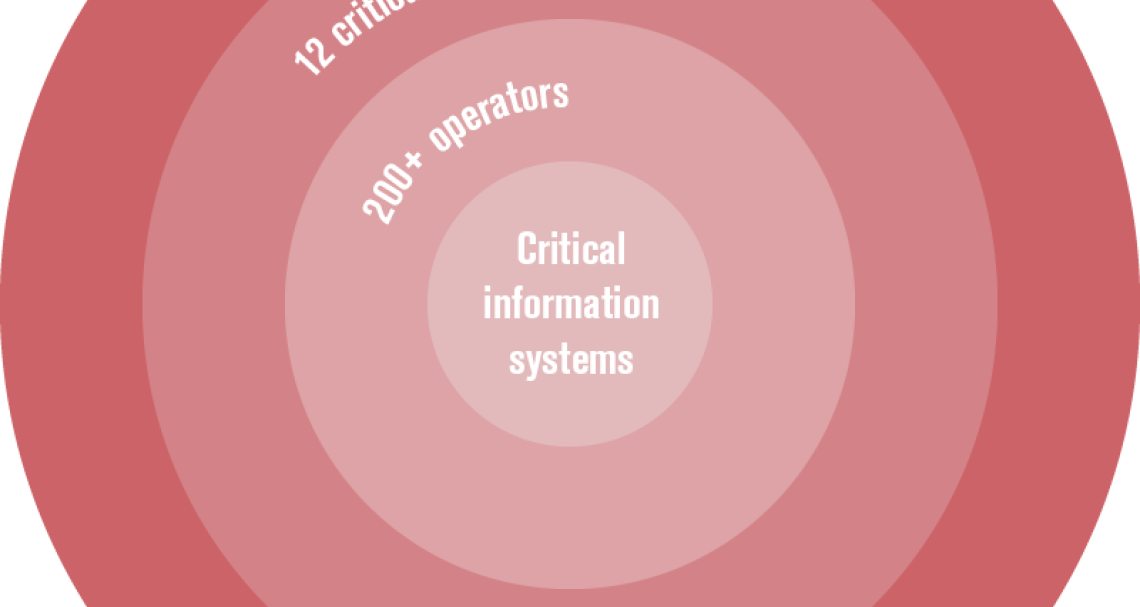
The CIIP law adopted in December 2013 in France drew onto an existing list of critical operators (called “operators of vital importance”) defined in France’s framework for the “security of activities of vital importance” established in 1998.
Defined by sectorial ministries in coordination with the General Secretariat for National Defence and Security this framework identifies more than 200 operators in 12 sectors including: Food, Health, Water, Telecom & Broadcasting, Space & Research, Industry, Energy, Transport, Finance, Civilian administration, Military activities and Justice.
Operators are defined as “operator[s] whose unavailability could strongly threaten the economical or military potential, the security or the resilience of the Nation”.
WHAT ARE “CRITICAL INFORMATION SYSTEMS”?
In the existing “security of activities of vital importance framework”, operators were asked to identify their critical “physical points”.
Considering that risks for the security information systems did not match the approach of “physical points”, the CIIP law required that operators identify their “critical information systems”.
These information systems are the ones supporting vital functions of the operators and “whose unavailability could strongly threaten the economical or military potential, the security or the resilience of the Nation”. Not every information systems of critical operators therefore falls within this category (e.g. SCADA systems, etc.).
Requirements of the CIIP law exclusively apply to these information systems.
Operators are responsible for identifying their critical information systems and provide ANSSI with a list of these systems.
WHAT ARE THE SECURITY RULES IMPOSED TO THE OPERATORS?
The security rules defined by ANSSI and the operators are preventive actions aiming at reducing the risks of success for most cyberattacks.
The rules were defined taking into account ANSSI’s and operators’ operational experience and existing international standards.
Mainly cross-sectoral, these rules mostly include cyber hygiene measures and fall within 20 categories:
- Information assurance policies
- Security accreditation
- Network mapping
- Security maintenance
- Logging
- Logs correlation and analysis
- Detection
- Security incidents handling
- Security alerts handling
- Crisis management
- Identification
- Authentication
- Access control and privileges management
- Administration access control
- Administration Systems
- Segregation in systems and networks
- Traffic monitoring and filtering
- Remote access
- Systems set up
- Indicators
HOW DOES SECURITY INCIDENT NOTIFICATION WORK WITHIN THE FRAMEWORK OF THE CIIP LAW?
Within the CIIP law, ANSSI shall be notified by operators of incidents occurring on their critical information systems.
Types of incidents to be notified have been specified by sectoral orders.
When handling these notifications, ANSSI must protect the confidentiality of the operator in a confidence building spirit.
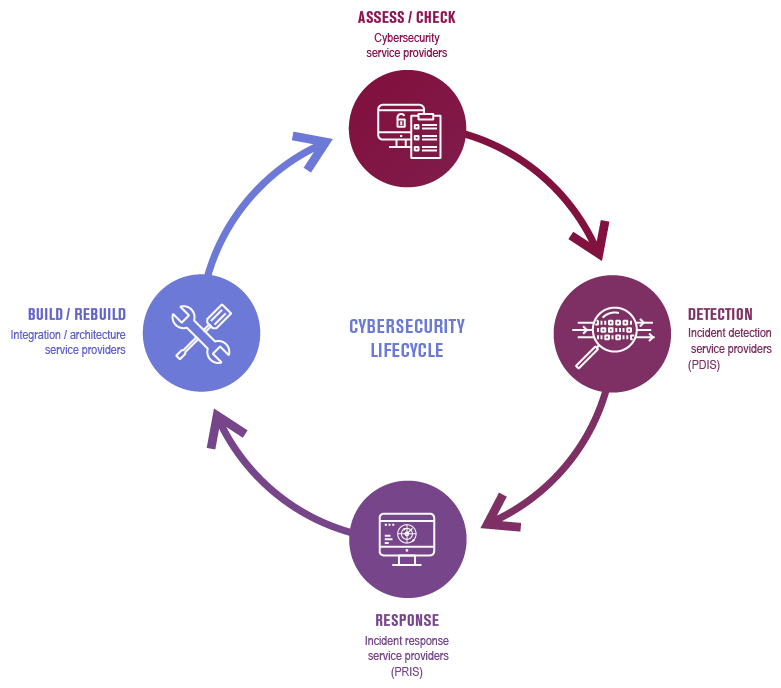
WHAT ARE CYBERSECURITY TRUST SERVICE PROVIDERS IN FRANCE?
In order to facilitate the implementation of the CIIP law by the operators having to fulfill new requirements, ANSSI has established a challenging and efficient process allowing the qualification of private “Trust Service Providers”.
Based on the savoir-faire of expert qualification bodies accredited by COFRAC* and licensed by ANSSI, a rigorous evaluation process allows the qualification of candidates providers meeting the adequate security and trust requirements.
These providers are qualified according to reference documents defined by ANSSI after public consultation and phases of experimentation The qualification process includes the assessment of skills of each consultant as well as the solidity of the companies.
4 types of services can be qualified, with the aim of covering the entire range of needs in the cybersecurity lifecycle:
- Cybersecurity audit service providers (PASSI) – 20 qualified / 14 on going
- Incident detection service providers (PDIS) – 8 ongoing (experimental phase)
- integration response services providers (PRIS) – 6 ongoing (experimental phase)
- Integration / architecture service providers (planned)
See the list of Qualified Trust Service Providers